Credits: 5EC
Motivation: To stay competitive, organizations continuously automate their processes and increasingly rely on information technology. The continuity of the business sometimes depends solely on the confidentiality, integrity and availability of the IT systems and the data they process. The security of IT systems is important for both the IT departments that are busy keeping the infrastructure running on a 24/7 basis and the senior management, to manage the risks to the organization and keep it profitable.
The challenge of managing information security in an organization is its multi-disciplinary nature. Operational staff needs to understand the capabilities of the infrastructure and the application layer and the potential vulnerabilities associated with them. The procurement staff needs to be capable to procure secure-by-design software and embed security requirements in the project stage gates. Finally, senior management needs to understand the implications of the security breaches to the business competitiveness and the business continuity, and the controls to improve the resilience of the organization against such events. To add to the complexity, computer systems can be compromised not only through exploitation of computer vulnerabilities and miss-configurations, but also through abusing the human aspect (eg. social engineering) and vulnerabilities in physical security. Developing a multi-layer protection that besides the technical and organizational, will also tackle the human and physical risks is a challenge and requires cooperation between the facility department, communication department, HR and the IT department.
Synopsis: Within the course we will explore information security and approach it from business, technical and academic perspective. From business perspective, the course will look into the common governance and management structures. The course will also explore new emerging areas and the implications of these systems in the supply chain and the safety processes. From technical perspective, the course will include topics on social engineering, phishing, penetration testing. During each lecture we will also point out the academic challenges for each of the topics and how is the academy responding to them. For example, the course will look at how organizations manage risks from socio-technical attacks and research done to identify, assess and remediate these risks.
Aim: The goal of this course is to introduce a number of security topics to 4TU Security Master students and BIT Master students and enable them to select and execute specific assessments for a number of security topics.
Learning outcomes: The student will:
- understand and explain the complexities of information security in a mature organization;
- have knowledge of the common models and standards for managing information security and to be able to apply this to real-world organizations;
- be familiar with the state of the practice and the state of the art in information security and be able to assess the position of an organization in this field;
- be familiar with the leading standards in this area, their shortcomings and practical implementation guidelines, and to be able to apply this on a given organization
- be able to map risk appetite to control objectives, control and guidance documentation, and to assess the compliance against control objectives using expert assessment and internal audit;
- understand the common risks and controls in information security;
- be able to do basic security assessments
Lecturers: Dr Vivian Jacobs(Deloitte), Dr. Alexandr Vasenev (UT), Dr. Maya Daneva (UT)
Examination: Individual exam on selected content (100%) with the option to boost the grade by writing a paper on a pre-defined sub-topic corresponding to the lecture topics. The grade of the optional paper counts for 10% of the total grade and is only taken into account if the grade of the paper is above a 5.5 score. The total grade is maximized at 10.
Contents: As part of the course, Deloitte will use its Cyber Security Management Framework and deep dive into a few topics for each of the Framework components.
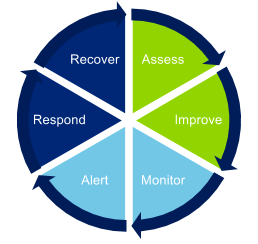
ASSESSMENT AND IMPROVEMENT CAPABILITIES
GOVERNANCE AND RISK MANAGEMENT - Managing and governing information risks. Risk management methodologies in the industry. Overview of the leading control frameworks. Compliance against security risks and reporting. Common pitfalls in implementation and research challenges.
IDENTITY AND ACCESS MANAGEMENT - Managing electronic identities in B2B and B2C and their importance to organizational security. Cross use of EI between government agencies and the financial sector. Potential business growth areas.
ASSESSMENT OF INDUSTRIAL CONTROL SYSTEMS - Introduction to ICS and trends and common security threats. Differences between managing the security of ICS and IT systems. Common challenges in ICS security and how organizations approach them. Live demonstration of an ICS attack.
PHYSICAL SECURITY AND SECURITY AWARENESS - The link between physical, digital and social security. Physical security controls. Social engineering. Methodologies for enhancing security awareness. Penetration testing. Research challenges and potential business growth areas. Short exercise.
ALERTING AND MONITORING CAPABILITIES
SECURITY MONITORING – Development and deployment of monitoring capabilities. Live demo (or visit of operational) security operations center (SOC).
MANAGED SECURITY SERVICES - Outsourcing and managing services involving operational security such as SIEM, Log Management, Layer 7 protection and SOC deployment. Design, implementation and maintenance of security solutions. Live demo.
RESPONSE AND RECOVERY CAPABILITIES
INCIDENT AND THREAT MANAGEMENT – Identification of potential threats and events of interest. Triage of threats and analysis of incidents. Response and escalation procedures and processes. Few cases from the industry and a live exercise jointly with the crisis management lecture.
CRISIS MANAGEMENT AND BUSINESS CONTINUITY- Developing agile response capabilities. Crisis management governance. Decision making, escalation and notification processes. Few cases from the industry. Live exercise.
Core text: Various papers from the literature, supported by a syllabus.